Check out our White Paper Series!
A complete library of helpful advice and survival guides for every aspect of system monitoring and control.
1-800-693-0351
Have a specific question? Ask our team of expert engineers and get a specific answer!
Sign up for the next DPS Factory Training!

Whether you're new to our equipment or you've used it for years, DPS factory training is the best way to get more from your monitoring.
Reserve Your Seat Today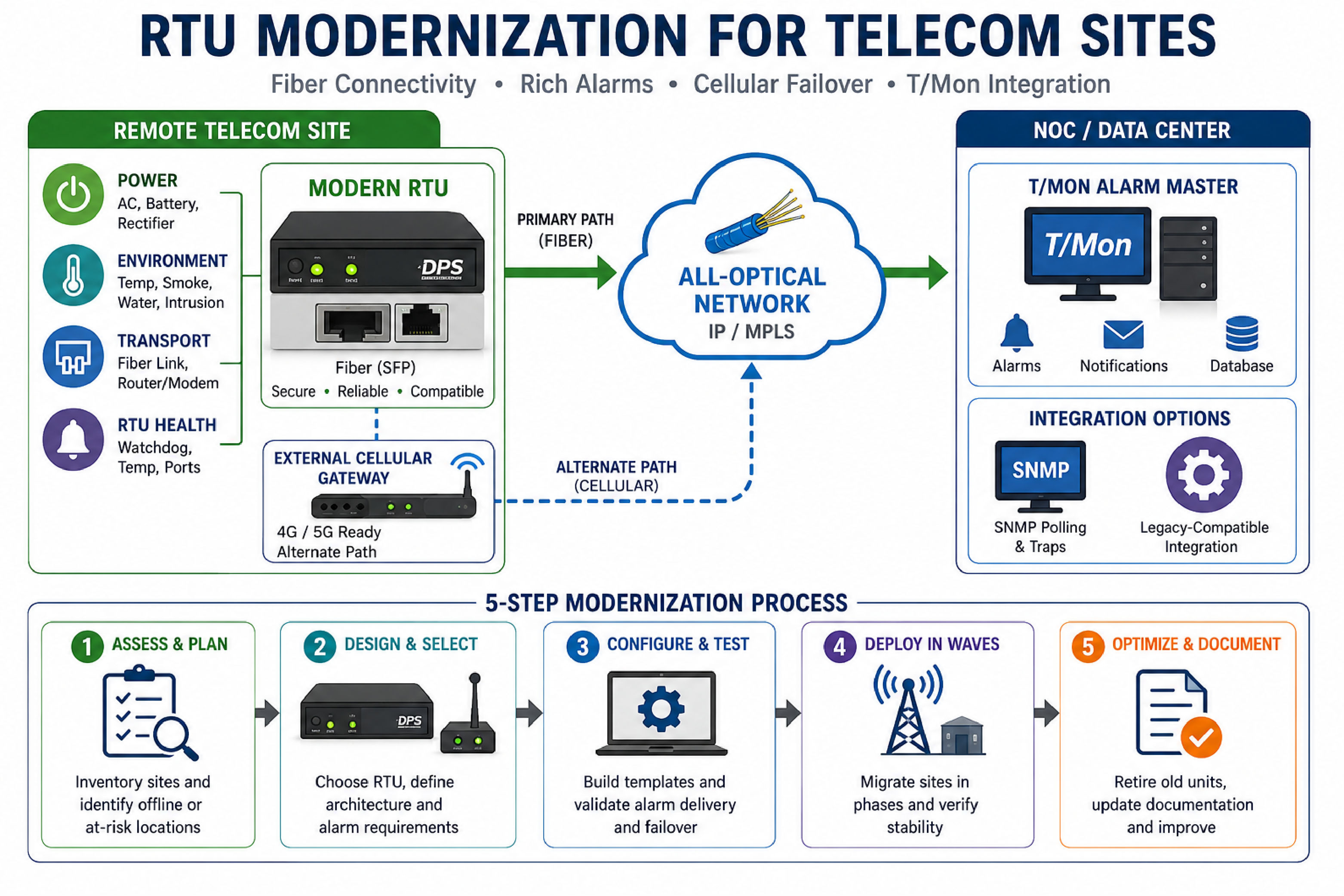
For infrastructure monitoring contexts, RTU modernization involves replacing or upgrading legacy remote telemetry units (RTUs) so they can communicate over current transport networks (such as all-optical fiber) while providing clearer alarms, stronger security, and maintainable hardware support.
Telecommunications operators often discover the need for RTU modernization when older units fail in the field, cannot interface with a new fiber-only transport design, or provide alarms that only say "site down" without explaining whether the cause is power, transport, or local equipment.
This article summarizes a common scenario for a regional telecommunications provider that had a mixed fleet of older RTUs and needed to restore visibility at multiple offline sites, add an alternate communications path, and plan a staged migration to current DPS Telecom platforms.
In telecom operations, a legacy RTU modernization project is usually triggered by the combination of hardware aging and network architecture change, where the monitoring endpoints no longer match the transport network, security requirements, or troubleshooting expectations.
A common pattern is that legacy RTUs were designed around copper Ethernet or T1 connectivity, but the operator migrates to an all-optical network where copper handoffs are no longer available at remote sites. When those sites go offline, the NOC sees loss of communication but cannot quickly distinguish between transport failure and local power or environmental issues.
Another trigger is supportability. When a device family is discontinued at the component level, some units become non-repairable even if they remain "supported" for configuration guidance. At that point, operators need a plan that reduces risk without forcing a disruptive rip-and-replace.
In NOC workflows, a "site down" alarm is an availability symptom, not a diagnosis. It indicates loss of communication or loss of a monitored heartbeat, but it does not identify whether the cause is commercial power, battery plant issues, fiber transport, a local router, or an RTU hardware fault.
When the alarm stream lacks root-cause context, the NOC must escalate to manual checks, dispatch site visits, or wait for field confirmation. This increases mean time to decide, which is different from mean time to repair but often drives the operational cost of an incident.
Improving alarm specificity typically requires two changes: (1) better on-site telemetry (power, environmental, door, generator, rectifier, and transport handoff status) and (2) a monitoring architecture that still delivers alarms when the primary path fails.
In telecom plant monitoring, an all-optical transport network changes RTU connectivity requirements by replacing copper handoffs (such as legacy copper Ethernet) with fiber-based interfaces, often delivered via SFP transceivers and fiber patching at the site.
If an RTU is limited to copper Ethernet, it may be physically unable to connect to the new transport network even if the rest of the site equipment is upgraded. Operators then face a choice: add media conversion (which can add complexity and failure points) or migrate to RTUs that natively support fiber interfaces.
Fiber compatibility is not only a physical-layer concern. It also affects the IP design and operations model, because sites may adopt new VLANs, routing, firewall policies, and security baselines during the transport cutover.
| Approach | What It Means | Operational Pros | Operational Risks |
|---|---|---|---|
| Keep copper-only RTU and add media converter | Fiber to copper conversion placed between transport handoff and RTU Ethernet | May preserve existing RTU configuration and workflows | Extra device to power, mount, secure, and troubleshoot; can become a new point of failure |
| Migrate to fiber-native RTU | RTU provides fiber connectivity (commonly via SFP-based ports) and current security | Cleaner architecture and reduced edge complexity; supports long-term lifecycle planning | Requires migration planning, testing, and possible monitoring database updates |
A staged RTU migration plan is a controlled process that replaces or upgrades monitoring endpoints site-by-site while keeping the NOC alarm workflow operational throughout the transition.
Staged migration is often required when an operator has a mixed fleet, including units that are end-of-life and units that remain supported. A staged plan reduces the risk of a wide-area monitoring outage and lets operations validate templates, points mapping, and failover behavior incrementally.
In DPS Telecom product planning, RTU replacement options are selected based on physical interfaces (fiber vs copper), the number and type of alarm inputs, security requirements, and the monitoring system used in the NOC.
In scenarios where older T1 and copper Ethernet RTUs are deployed, a fiber-capable replacement is often required to connect directly to modern transport. One common approach is migrating from copper-focused legacy units to a fiber-based RTU model that supports SFP ports.
In a monitoring endpoint, "future-ready" means the platform can meet current security policy and can expand with additional sensors and sites without forcing a new hardware cycle.
In infrastructure monitoring procurement, a modernization program refers to a vendor-supported process that helps operators replace aging endpoints while minimizing operational disruption and managing the transition cost of retired hardware.
For legacy fleets that include discontinued units, a trade-in credit approach can be paired with staged cutovers so that operators can prioritize the most at-risk sites first, then continue systematically.
Modernization programs also create a structured way to document which legacy units are discontinued, which are supported only for configuration guidance, and which are still fully supported. That clarity helps NOC leadership and field operations align on a realistic spares and repair strategy.
In telecom monitoring, cellular failover is an alternate communications path that allows an RTU to report alarms and accept management access when the primary network transport is unavailable.
A practical design choice is whether cellular connectivity is embedded inside the RTU or provided by an external cellular gateway. A common modern recommendation is to use an external cellular gateway connected via Ethernet to the RTU. This makes the cellular component easier to upgrade when carrier technology shifts from 4G to 5G, and it can allow standardization across multiple RTU models.
External cellular is also useful when an operator wants a consistent security and routing policy at the edge, because the cellular gateway can be managed as a network device with its own firewalling and VPN capabilities, depending on the selected model and carrier plan.
In NOC monitoring architectures, compatibility refers to how a new RTU presents alarms, points, and protocols to an existing alarm master and database so that operators can continue to use established screens, filters, and escalation workflows.
DPS Telecom environments often include T/Mon as the alarm master, with a database that defines site points, naming conventions, and notification rules. During an RTU refresh, operators usually want new hardware to integrate without requiring an immediate rebuild of the monitoring database.
One approach used in migrations is a "legacy mode" where a newer RTU generation can appear similar to an older generation for core monitoring functions. This can reduce the initial integration burden, while still enabling a path to adopt newer features later.
In network and facility monitoring, SNMP integration means using SNMP polling and/or SNMP traps to exchange status and alarms between an RTU and the monitoring system, rather than relying on older proprietary or legacy integration methods.
SNMP is often considered during modernization because it can expose a broader set of device capabilities, supports standardized security with SNMPv3, and can simplify integration with multiple tools when organizations have both an alarm master and network management systems.
For operators evaluating a newer RTU generation, a key question is whether direct SNMP integration enables access to the full feature set, compared to operating the RTU in a legacy-compatible mode for the existing alarm master.
| Decision Factor | SNMP-Based Integration | Legacy-Compatible Integration |
|---|---|---|
| Speed of initial cutover | May require new MIB review, trap handling, and point mapping | Often faster when it matches existing templates |
| Access to advanced device capabilities | Often better for exposing newer telemetry and configuration options | May limit newer features to what the legacy profile supports |
| Security controls | SNMPv3 supports authentication and encryption | Depends on the legacy method; may be more limited |
| Tool interoperability | Can support integration with multiple systems if designed carefully | Typically optimized for one alarm master workflow |
In mission-critical site monitoring, "good" root-cause visibility means the NOC can determine the most likely failure domain within minutes, using alarms that are specific, time-correlated, and delivered reliably even during partial network outages.
Good visibility is not only about adding more alarms. It is about selecting the right alarms, organizing them into an operational model, and ensuring the transport design delivers those alarms under realistic failure scenarios.
In telecom monitoring programs, integration means combining edge RTUs, alarm transport paths, and an alarm master into one operational system that delivers actionable alarms and supports repeatable deployments.
DPS Telecom typically supports these programs by helping operators evaluate replacement RTU families (including fiber-capable options), validate compatibility with the existing T/Mon environment, and design alternate-path communications using external cellular gateways where appropriate.
DPS Telecom also helps translate modernization goals into configuration standards, including point naming, thresholds, security configuration, and SNMP strategy. This is especially important when a fleet includes multiple generations of devices and the operator wants to avoid inconsistent alarm behavior between sites.
What is the main reason older RTUs go offline after a fiber network upgrade?
The most common reason is physical interface mismatch. A copper-only Ethernet RTU cannot directly connect to a fiber-only handoff without additional equipment such as a media converter.
Is it better to build cellular into the RTU or use an external cellular gateway?
An external cellular gateway connected via Ethernet is often preferred because it can be upgraded independently as carriers move from 4G to 5G, and it can be standardized across multiple RTU models.
Can a newer RTU generation be integrated into an existing T/Mon system without rebuilding everything?
Many migrations use a compatibility approach, such as operating the RTU in a legacy-compatible mode for core functions. A database review is still recommended to confirm point mapping and backups.
Does SNMP integration provide access to more RTU features than legacy integration?
SNMP integration can expose more capabilities, especially when SNMPv3 is used for secure telemetry. The exact feature difference depends on the device profile and how the alarm master consumes the data.
How do you confirm that an alternate path will work during a real outage?
Alternate-path designs should be tested with controlled failover scenarios, verifying alarm delivery, remote access, and the return-to-primary behavior when the main transport is restored.
What should be documented before replacing end-of-life RTUs?
At minimum, document the site inventory, point list, current monitoring templates, transport interfaces, power and environmental sensors, and where the monitoring database is hosted and backed up.
If legacy RTUs are blocking fiber transport upgrades, limiting root-cause alarms, or leaving sites unreachable during outages, DPS Telecom can help design a staged modernization plan with compatible RTUs, T/Mon integration, and external cellular failover options.

Andrew Erickson
Andrew Erickson is an Application Engineer at DPS Telecom, a manufacturer of semi-custom remote alarm monitoring systems based in Fresno, California. Andrew brings more than 19 years of experience building site monitoring solutions, developing intuitive user interfaces and documentation, and opt...