Check out our White Paper Series!
A complete library of helpful advice and survival guides for every aspect of system monitoring and control.
1-800-693-0351
Have a specific question? Ask our team of expert engineers and get a specific answer!
Sign up for the next DPS Factory Training!

Whether you're new to our equipment or you've used it for years, DPS factory training is the best way to get more from your monitoring.
Reserve Your Seat Today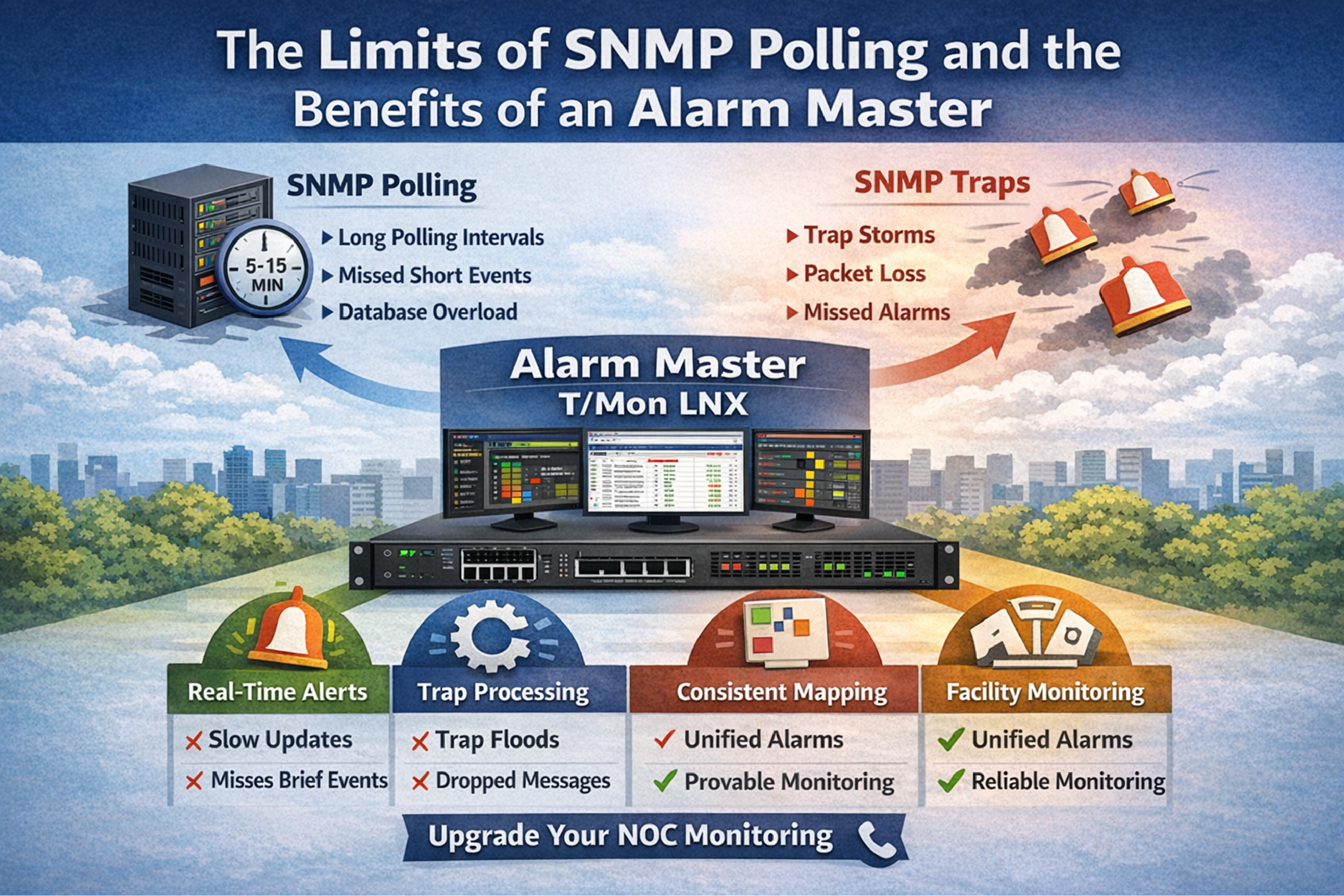
SNMP-based alarm monitoring refers to using SNMP polling and/or SNMP traps to detect status changes in network elements and remote site devices, then converting those events into actionable NOC alarms. SNMP works well at small scale, but many organizations eventually hit practical limits in their monitoring platform when device counts grow, alarm tables expand, or trap storms occur.
This article explains common failure modes in SNMP polling and trap processing, why missed alarms happen in real NOC workflows, and what a more reliable architecture looks like. It also describes how an alarm master approach, such as DPS Telecom T/Mon LNX paired with SNMP trap processing, is commonly used to improve reliability and prepare for expansion into facilities alarms like HVAC, generator, and power monitoring.
SNMP polling is defined as a monitoring system periodically querying devices for specific OIDs (or tables) and then evaluating the returned values to determine alarm states. Polling is deterministic in timing, but it is limited by polling intervals, database growth, and the ability of the monitoring platform to consistently execute every query.
In a typical environment with hundreds of remote monitoring units and sensors (for example, temperature monitors and RTUs collecting discrete and analog points), a polling-based approach often becomes a compromise between timeliness and system load. Poll too often, and the monitoring platform or database can become the bottleneck. Poll less often, and short-duration alarms can be missed.
A key architectural point is that a polling engine has two jobs at once: collect data and evaluate alarm logic. When the collector is overloaded, it is common for alarm evaluation to lag or for collection to be skipped, which can look like the alarm never happened.
A short-duration alarm is defined as an alarm condition that asserts and clears between polling cycles. If the monitoring system samples a point every N minutes, any event that occurs and resolves within that window may never be observed.
This pattern is common in remote site operations:
Even if the remote device logs the event locally, the NOC may not see it if the monitoring design relies only on periodic sampling. For this reason, many teams supplement polling with event-driven notifications (SNMP traps) or use an alarm master that can receive and normalize events immediately.
SNMP table polling is defined as collecting an indexed set of OIDs (rows and columns) that represent a device's alarm or status table. Table polling can provide a complete view of alarm state, but it can also multiply data volume quickly, especially when the monitoring platform stores every poll result as a time-series record.
At scale, table polling can produce runaway database growth and performance degradation. Teams often respond by switching from full table polling to polling only a small set of critical OIDs. That reduces load, but it also creates operational tradeoffs:
When the monitoring system becomes dependent on custom queries, failures can be hard to detect. A query can stop running, a scheduled job can hang, or a credential can expire, and the result is not always an obvious platform alarm. Operators may only discover the issue after a missed incident.
An SNMP trap is defined as an event-driven message sent by a device to a management system when a condition changes. Traps can reduce the need for frequent polling and can capture short-duration events, but trap handling has its own failure modes.
Traps can be missed when:
Trap-based monitoring is most reliable when it is designed as an event ingestion pipeline rather than as a best-effort message stream. That usually means: dedicated trap processing, consistent mapping, rate-handling strategy, and a clear method to reconcile trap events with current state (often via light polling, periodic audits, or device-side alarm tables).
Deployment standardization is defined as using consistent templates for point naming, severity, alarm descriptions, and OID/trap mapping across sites and device families. Without standardization, two identical physical conditions can produce two different alarms in the NOC.
When remote site fleets expand over time, it is common to see mixed configurations across device types, firmware revisions, and site builds. The operational impacts are measurable in day-to-day work even when the underlying devices are functioning correctly:
For environments that include devices such as TempDefender and NetGuardian LT units (or similar environmental monitors and RTUs), the long-term win is to treat alarming as a program: standard templates, lifecycle control, and a central system that enforces mapping consistency.
An alarm master is defined as a central system that ingests alarms from many sources, normalizes them into a consistent alarm model, applies correlation and routing rules, and presents operators with a reliable, deduplicated view of active conditions. In many telecom, utility, transportation, and industrial NOCs, the alarm master is the system of record for alarms, while other tools handle performance metrics, configuration management, or ticketing.
DPS Telecom T/Mon LNX is an example of an alarm master platform that can be used to improve reliability and flexibility in SNMP-centric environments. A typical approach is to use T/Mon LNX as the authoritative alarm presentation and workflow engine, while integrating with existing tools where appropriate.
An SNMP trap processor is defined as a component that receives traps/informs, validates and parses them, maps them to defined alarm points, and can optionally respond to queries or acknowledgments depending on the workflow. In high-volume environments, separating trap ingestion from general-purpose monitoring tasks reduces the risk that one subsystem overload affects alarms.
Many organizations also need to support multiple SNMP versions:
DPS Telecom commonly recommends pairing T/Mon LNX with an SNMP Trap Processor and Responder package (supporting v1, v2c, and v3) when the goal is to improve event-driven alarming without relying on a general-purpose NMS to do everything at once.
Monitoring architecture selection is defined as choosing how alarms are collected, how state is represented, and how operators interact with active conditions. The right choice is usually a blend, but it helps to compare the strengths and failure modes directly.
| Approach | Best For | Common Failure Mode | Mitigation |
|---|---|---|---|
| SNMP polling (OID-based) | Periodic health checks and steady-state values (temperature, voltage) | Missed short-duration events; collector overload increases latency | Shorten intervals selectively; offload alarms to event-driven ingestion |
| SNMP table polling | Full state capture when data volume is manageable | Database growth and query pressure; hard-to-maintain logic | Limit tables; store state efficiently; use an alarm-focused system |
| SNMP traps | Immediate notification, including brief events | Trap floods and UDP loss; inconsistent mapping across devices | Dedicated trap processing; normalization templates; auditing |
| Alarm master (e.g., T/Mon LNX) | Operational alarm workflow, correlation, and consistent presentation | Upfront integration and point mapping effort | Phased migration; standard templates; validate with test plans |
A phased migration is defined as moving alarm sources and operator workflows to a new system in controlled steps, while keeping the existing platform running until acceptance criteria are met. This reduces the risk of missing alarms during transition.
A practical phased plan for SNMP-centric alarm environments often looks like this:
For remote site fleets that include environmental monitors and RTUs, migration planning should include how facilities points (HVAC, generator, power) will be represented in the same alarm taxonomy as network element alarms. This is where an alarm master can prevent tool sprawl and reduce operator context switching.
NOC platform power configuration is defined as selecting the appropriate power input design for the alarm master server so it matches the facility power environment. Many NOC and telecom environments standardize on either AC feeds or -48VDC plants.
Two common configuration directions for T/Mon LNX include:
In addition to the base T/Mon LNX system, deployments often include an SNMP Trap Processor and Responder package to improve trap ingestion and standardize SNMPv1, SNMPv2c, and SNMPv3 handling. Annual maintenance is typically considered as part of operational planning to keep software, support, and update pathways current.
A unified alarm strategy is defined as representing network, power, and environmental conditions in a single operational alarm model so operators can triage incidents without switching tools. Devices such as NetGuardian LT RTUs and TempDefender units commonly provide the physical inputs for that strategy: discrete contacts, analog readings, and environmental sensors.
In many organizations, these remote devices are already deployed widely, but the monitoring architecture is the constraint. An alarm master approach can help by:
DPS Telecom systems are commonly used as the integration point where SNMP traps, RTU point states, and operator workflows meet. This is especially helpful when a NOC needs to support both network element alarms and facilities alarms with the same staffing and escalation processes.
A mature SNMP alarm monitoring design is defined as one that maintains alarm integrity under load, provides immediate visibility for critical events, and is simple to operate during stressful incidents. The goal is not to eliminate polling or traps, but to remove single points of failure in alarm ingestion and alarm presentation.
| Design Area | Decision Question | Recommended Direction |
|---|---|---|
| Alarm ingestion | Do you need to capture brief events? | Use traps/informs with dedicated trap processing; add polling for reconciliation |
| Alarm presentation | Is the tool optimized for operator workflow and alarm state? | Use an alarm master (e.g., DPS Telecom T/Mon LNX) as the system of record |
| Standardization | Do sites use consistent point naming and severity? | Create templates per device family; enforce during deployment and change control |
| Performance and data | Is the monitoring database growing due to table polling? | Reduce table polling; store alarm state efficiently; keep time-series for trends only |
An NMS is typically defined as a platform focused on discovery, performance metrics, and device management, while an alarm master is defined as a system focused on alarm ingestion, normalization, correlation, acknowledgment, and operator workflow.
Critical alarm coverage is usually defined as event-driven capture plus state verification. Traps provide immediacy and capture short events, while targeted polling can confirm current state and detect trap delivery problems.
Preventing silent monitoring failures is defined as alarming on the monitoring pipeline itself. This includes watchdog alarms for collectors and scheduled jobs, plus a design that reduces dependence on fragile custom queries.
Trap storm handling is defined as maintaining ingestion under load and presenting alarms in a usable way. This can include dedicated trap processing, rate handling, normalization, and correlation rules that reduce duplicates.
SNMPv3 relevance is defined as whether the environment requires authenticated and encrypted SNMP for compliance and security policy. Many organizations standardize on SNMPv3 where supported, while maintaining v2c for legacy devices.
A practical first step is defined as identifying which events are short-duration and confirming whether the current design can observe them. Often the next step is enabling event-driven alarming (traps/informs) and validating ingestion under load.
If your NOC is seeing missed alarms, database overload from SNMP table polling, or unreliable trap handling during high-load conditions, DPS Telecom can help design an alarm architecture that scales. We can recommend an approach using T/Mon LNX as an alarm master, plus SNMP trap processing and standardized point mapping for RTUs and environmental monitoring.

Andrew Erickson
Andrew Erickson is an Application Engineer at DPS Telecom, a manufacturer of semi-custom remote alarm monitoring systems based in Fresno, California. Andrew brings more than 19 years of experience building site monitoring solutions, developing intuitive user interfaces and documentation, and opt...